Enterprise IT management is a constantly evolving environment and requires constant diligence to make sure systems are secure and functioning efficiently. In today's modern digital world, IT engineers must keep their environment up to date with patches, encryption methodologies, security tools, intrusion detection techniques, etc. – all while keeping end-users happy.
Gartner has released their analysis guide for security orchestration, automation, and response (SOAR) solutions to highlight how organizations should adopt this tech. The 1E Platform enables IT personnel to improve the efficiency of their solutions by automating policies. This streamlines compliance across all devices, ensuring they're secure, stable, and performant.
Our ease of "customer-configured compliance automation" is a key differentiator of the 1E Platform versus other digital employee experience (DEX) tools. Endpoint Automation allows administrators to enforce policies to guarantee:
- Services are configured correctly and running
- USB storage device usage is blocked
- Local Admin rights are granted or removed
- SCCM ConfigMgr / Intune dependencies are configured
- Encryption is monitored and/or enforced
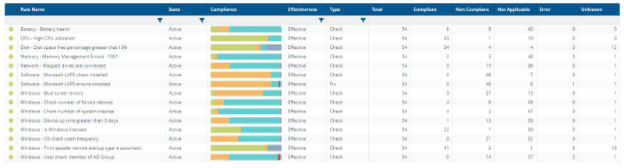
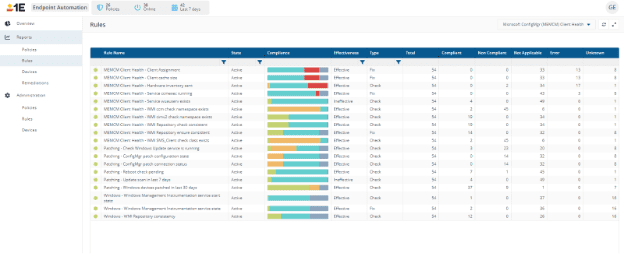
Within the 1E Endpoint Automation module, administrators can quickly create rules and policies to ensure compliance of all endpoints. These policies even enforce compliance when an endpoint is offline. Dashboards then give admins a view of how compliance, and remediations, are affecting the enterprise.
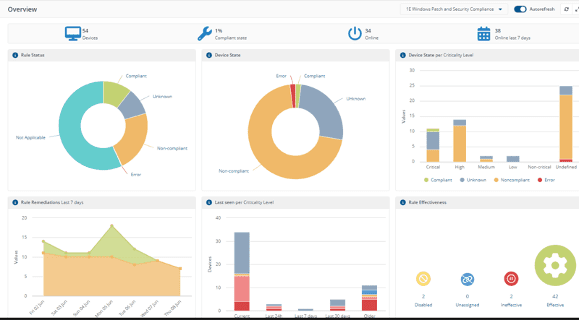
Compliance is also critical in maintaining Device Health in the Enterprise. Making sure memory, CPU, disk, and network subsystems are correctly utilized is imperative to keeping your end-users happy. Alerting when resources are over-consumed enables proactive management in an Enterprise environment. Checking how your endpoints are performing and viewing compliance data is crucial to maintaining a healthy DEX environment.
Rules and policies in endpoint automation
Endpoint Automation rules are in the 1E Platform, with more available online in our DEX Store. A huge benefit of the 1E Platform is the ability for customers to develop and create their own rules and policies. There is a GUI environment to build out rules to check on compliance and, if necessary, 'fix' endpoints to guarantee compliance. Rules can either be a 'Check' rule to alert if a machine isn't in compliance with a specified setting, or a 'Fix' rule to automatically correct the setting on the endpoint. Rules are created with:
- Preconditions
- This will determine whether the Rule you are creating applies to a device. If the Precondition isn't met, the Check won't execute. If you don't specify a precondition, this Rule applies to all devices.
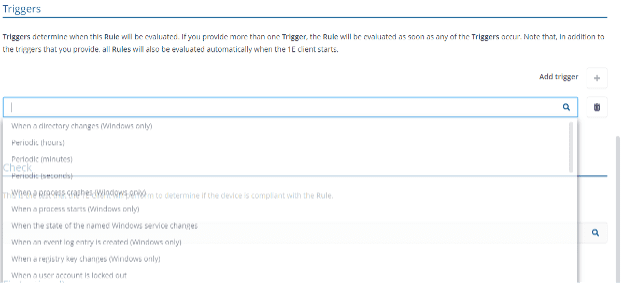
- Triggers
- Triggers determine when this Rule will be evaluated. If you provide more than one Trigger, the Rule will undergo evaluation as soon as any of the Triggers occur. Note that, in addition to the triggers that you provide, all Rules will also be evaluated automatically when the 1E client starts.
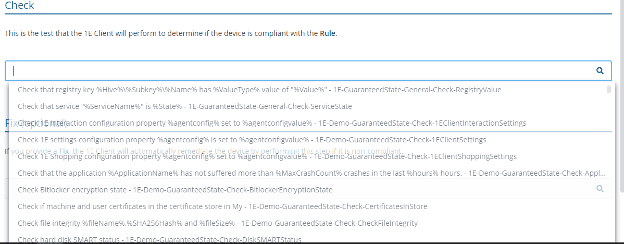
- Checks
- This is the test that the 1E Client will perform to determine if the device is compliant with the Rule.
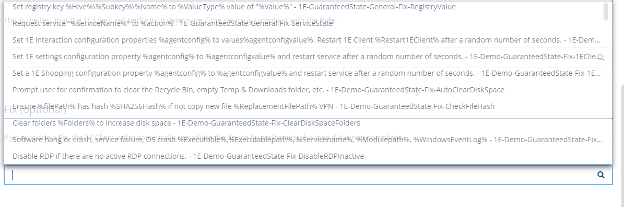
- Fix
- If you provide a Fix, the 1E Client will automatically remediate the device by performing this step if it is non-compliant.
Rules are created with the above parameters and placed into policies that are then assigned to Management Groups within the enterprise. These rules and policies take effect even when a machine is offline and not connected to the internet. The 1E Client Agent keeps the rules local, maintaining compliance at all times.
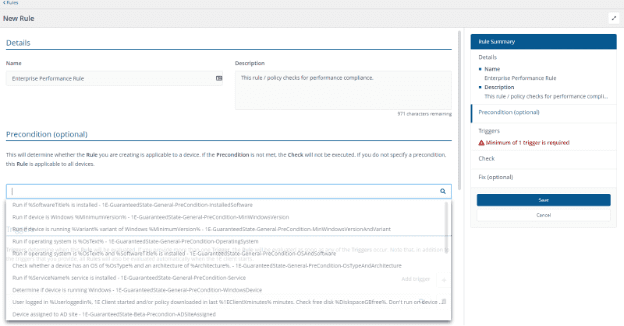
The ability for administrators to quickly create rules and apply them to Management Groups (collections of endpoints) within 1E Endpoint Automation is a huge differentiator in the DEX field. This is just one of the reasons that Gartner called the 1E Platform a 'Remediation Powerhouse'!
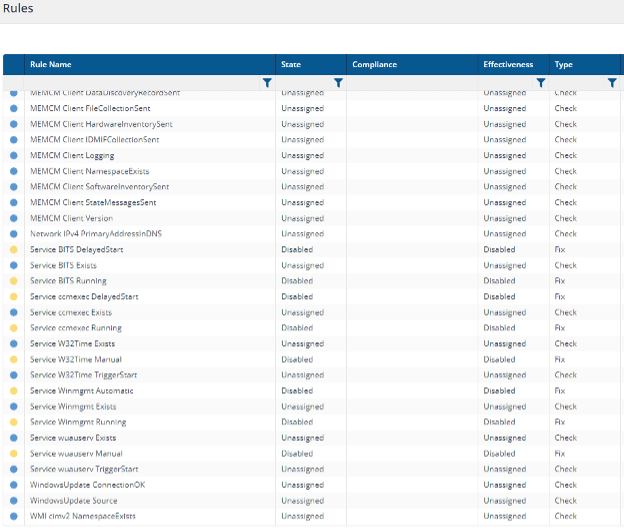
ConfigMgr health
One of the primary reasons that enterprise administrators see operating system health metrics fall is that patching of the OS (Operating System) isn't current. This impacts the stability of the OS as well as causing security implications. Microsoft ConfigMgr administrators need a way to make sure the endpoint is healthy, and that it can pull down patches and updates. 1E enables this with another Automation Compliance Policy for MEMCM Client Health. This policy's rules check and fix settings such as:
- SMS Agent Host Service parameters
- Windows WMI (Windows Management Instrumentation) Repository settings and health
- ConfigMgr Client Site Settings
- ConfigMgr Hardware and Software Inventory settings
- Windows Update Connection status
- Windows Time (Win32 Time) service settings
All these settings, and more, are quickly configured through the rules associated with MEMCM Client Health within 1E Endpoint Automation. Reporting analytics will alert administrators when, and if, machines are compliant with these policies, and if enabled, the 'fix' rules will enforce the settings on the endpoints.
All of this is to enforce stability and security of the endpoints and to ensure that the endpoints can successfully download patches and updates from the ConfigMgr or WSUS update points.
Security compliance
As in the topics above, compliance on endpoints is critical. Security compliance should be one of the top drivers for administrators in any enterprise environment. Ensuring your endpoints are secure with updates, have encryption settings configured correctly, communication ports and parameters are secure, and USB Storage Device access is managed correctly. All of these settings, and more, are configurable in the Device Security Compliance within Endpoint Automation. Settings such as:
- BitLocker Encryption
- Certificate expiry dates
- Credential Guard / Device Guard settings
- Device Domain Joined
- RDP (Remote Desktop Protocol) Enabled/Disabled
- SecureBoot settings
- SMB communication settings
- USB Mass Storage Settings
- Windows Defender Configuration
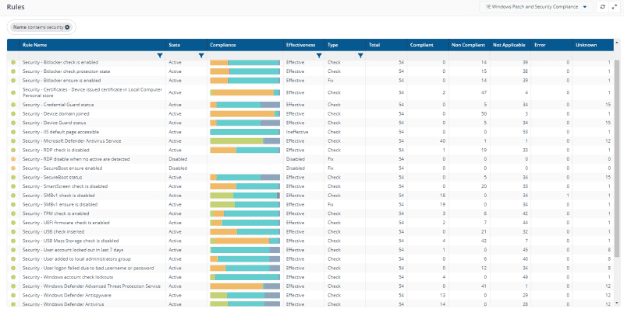
Complexities in a modern enterprise network are impossible to manage if using 'old-school' techniques and processes. The 1E Platform enables admins to be proactive in management, automate processes and remediations, and efficiently report on compliance data. Once these settings are enabled and deployed to the endpoints, the settings are enforced whether the endpoints are online or offline. 1E has an enormous library of rules and policies for our customers to implement in their environments.
Our 'Rule Builder', as detailed above, enables customer customization without having to go back to the 'vendor' and have them build a proprietary script for enforcement. Our 'Click and Build' GUI enables administrators to focus on the settings important in their environment and quickly deploy policies to enhance device security and device health. Endpoint Automation is just one part of the 1E Platform but enforcing compliance is critical in every enterprise network!




