It’s midnight. Do you know where your credentials are?
The recent Petya malware attacks are a reminder that malware relies on being able to propagate from a single point of infection across entire networks. While vulnerabilities such as the recent SMB v1 ‘EternalBlue’ exploit enabled WannaCry to propagate, Petya’s copycat ability to exploit this weakness was in many cases stymied by organizations having disabled SMB v1 and having also patched the underlying vulnerability.
Yet despite this, Petya still managed to spread with frightening rapidity. It did this by using the oldest trick in the malware author’s book – stealing credentials.
Credentials – user logins and passwords – are unfortunately easy for malware to steal. And the easiest credentials to steal are any account passwords which happen to be resident in memory. Malware scans memory looking for these passwords and harvests them. It’s like picking up a bunch of keys in the street and then trying every door in a row of houses to see if any of the keys will let you in. If they do, you can burgle the house, and possibly steal more keys, repeating the process indefinitely.
Now it’s hard to stop malware scanning memory. If you’re running Windows 10 Enterprise or Windows Server 2016, a new Microsoft feature, Credential Guard, is intended to make it a bit harder for malware to steal passwords by locking credentials away inside a sandboxed virtual environment.
However, even with Credential Guard, you can’t be sure that third-party software always manages credentials securely. Unless the application developers are very careful, it’s easy to leave sensitive passwords in device memory where malware can steal them.
There are things you can do, though, to mitigate the impact of credential theft. Here are five golden rules for keeping your precious credentials from being used as an attack vector.
Rule 1. Keep a watchful eye on local accounts

You should be proactive in controlling the proliferation of local accounts on your devices. Local accounts, as the name suggests, are specific to the device, as opposed to domain accounts which are global to your domain.
You should minimize the number of local accounts, and in particular, tightly control local accounts which are also members of the administrator's group on the device.
Importantly, you should never set up local accounts on devices where the password and account names are the same across devices. When you do this, you guarantee that malware can use those stolen credentials to compromise other devices.
Consider, instead, using Microsoft LAPS to manage administrator-privilege local accounts. LAPS ensures that account passwords are never shared, yet still allows domain administrators to access local device accounts as necessary.
Rule 2. Don’t forget about cached domain accounts
When you take your laptop home for the weekend, it’s handy that you can still log on using your domain credentials, even though the laptop isn’t connected to the corporate network. This magic works because your login name and the hash of your password are stored in the device registry. Windows stores up to 10 distinct logins by default, and these are never erased.
Now, this information is encrypted but unfortunately, that process has been reverse-engineered so it’s easy for malware to get these credentials. Apart from then being potentially able to directly use the password hash (so-called ‘pass the hash’ attacks), there’s nothing to stop the malware exfiltrating the hash back up to a command and control center, where banks of high-powered graphics cards can be used to ‘brute force’ crack password hashes, often in only a few hours.
At this point, the bad guys have your credentials and can do what they like with them.
To stop this, you need to do two things:-
- Ensure any mobile devices have full disk encryption enabled. If you don’t do this, anyone who can get physical access to the device can steal the credentials.
- Consider disabling domain account caching on server devices. If the device never disconnects from the corporate network, do you need cached credentials stored on it?. If not, you can use Group Policy to disable it.
Rule 3. Think carefully about running services on devices using domain account credentials
Some organizations consider this ‘best practice’ but be aware that the passwords associated with these credentials are stored in plain text in the device registry – so it’s easy for malware to steal these credentials.
Rule 4. Don’t forget the Windows credential store
From the Windows control panel, select Credential Manager to view the Windows credential store.
It’s probably somewhere you’ve never visited before, but all sorts of interesting credentials get stored here – by lots of different pieces of software – and it’s not very difficult for malware to steal any of them. Make sure you carefully control what’s stored in here.
Rule 5. Don’t forget plain old files
It’s not unknown for plaintext credentials to be stored in text files. Malware can easily scan your disk looking for interesting data – so make sure you keep sensitive information encrypted. If your company writes its own applications, make sure your developers know how to use Windows subsystems like DPAPI, the Data Protection API, to keep sensitive information encrypted when it’s stored in files.
Managing credentials with Tachyon
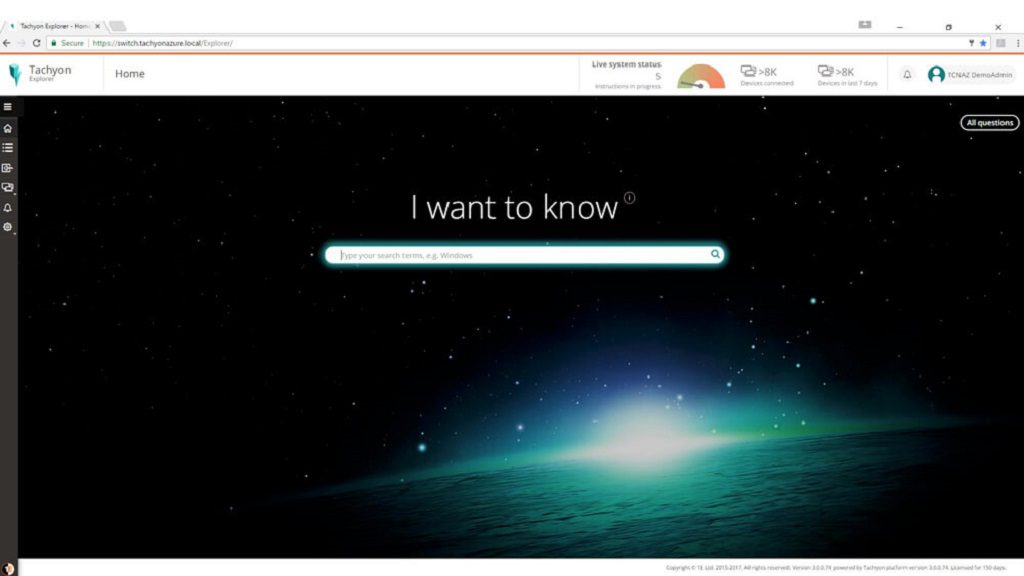
Tachyon makes it easy to get on top of credential management. With Tachyon you can not only review all local device accounts, you can also check out the cached domain accounts across your system, look at the contents of the credential store across your estate and also search files for patterns like ‘password’ at high speed.
And, naturally, you can verify which devices have full disk encryption enabled as well.
So make sure you know where your credentials are and keep yourself safe from malware attacks with 1E and Tachyon!



