This is the fifth and final blog in a series based on TriCon Elite Consulting’s recent review of the following Configuration Management tools:
- Group Policy
- PowerShell DSC/Azure Automation
- Endpoint Management Compliance MGR
- 1E Tachyon Guaranteed State
Our first blog examined TriCon Elite’s analysis of these vendors’ policy engines, and the second instalment explored these Configuration Management tools’ delivery of custom scripts. Part three focused on remediation capabilities, and last week was a comparison of administration. This fifth and final blog is about industry solutions and considers:
- Availability
- Customization
- Templating
- Installation
- Support
Overview:
TriCon looked at 3rd party products available for the four management tools, that augment the Compliance Settings capability in some manner.
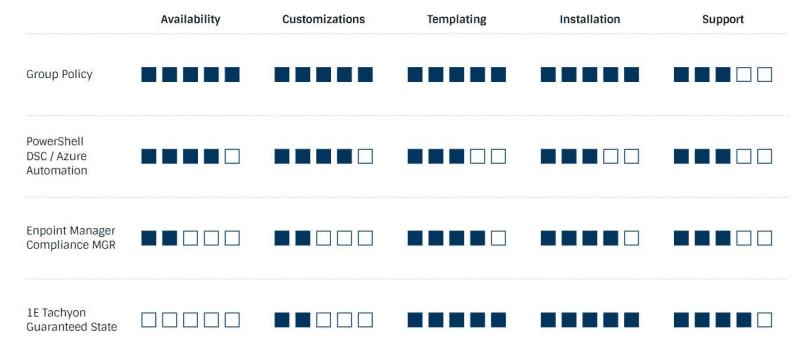
Availability
TriCon’s verdict: Group Policy took the lead in this category, and the report offers three examples of industry solutions that extend the native Group Policy Client Engine cross-platform; MicroFocus NetIQ AD Bridge, Beyond Trust AD Bridge, and Policy Pak by fellow Microsoft MVP Jeremy Moskowitz. Similarly, for PowerShell there are over 1800 authored resources available via the PowerShell Gallery, and custom CIs are available for download from many community blogs for Microsoft Endpoint Manager Configuration Manager (MEM-CM). Tachyon Guaranteed State scored lower here due to the policies' certificate requirements meaning the only external source for enhancements to the product is through the Tachyon Exchange, where requests can be made for different types of instructions, checks, fixes, and packs.
Customization
TriCon’s verdict: The report finds that customization options are available across the board. With Group Policy, the Center for Internet Security (CIS) offers Build Kits for specific technologies to assist in the automation of hardening systems. For Windows, Build Kits are distributed via importable Group Policy Objects (GPOs) and can be customized templates that serve as the baseline configuration for a Standard Operating Environment (SOE) build. PowerShell is fully customizable, and developers can either start with configurations from the PowerShell Gallery or build, customize, and publish their own. Endpoint Manager and Guaranteed State scored lower in this category, though the report highlights that for Endpoint Manager there are a number of 3rd party organization tools that augment the Compliance Settings process; and for Guaranteed State all policies available on the Tachyon Exchange can be imported into your local instance of TIMS, modified and re-signed with your own certificate, then made available to your endpoints.
TriCon also note that many of the policy fragments that are created by 1E are reusable, allowing for rapid development and customization of code.
Templating
TriCon’s verdict: Tachyon Guaranteed State and Group Policy are joint for highest score in this category. Guaranteed State policies are .zip files comprised of .xml files. Standard policies are available to be downloaded from the Tachyon Exchange. If modifications are not required, the policies can be directly imported and deployed without re-signing with your organization's code-signing certificate. Both PowerShell and Endpoint Manager scored well with regards to templating, however.
Installation
TriCon’s verdict: Tachyon Guaranteed State and Group Policy scored highest with regards to installation. For Guaranteed State, the report explains that a Solution Accelerator is provided for customers implementing multiple products that will streamline the deployment and configure product interoperability. When it comes to Group Policy, 3rd party solutions are installed by extending the default Group Policy Editor. In the case of the Center for Internet Security (CIS) templates, these are imported into existing Group Policy Objects created by an administrator. Installation of PowerShell Desired State (DSC) modules is typically done from the PowerShell Gallery, and for Endpoint Manager external CIs and Baselines are imported into MEM-CM using the native console option. However, PowerShell can also be used to import configuration items.
Support
TriCon’s verdict: TriCon found all four solutions to have effective support capabilities, though Tachyon Guaranteed State ranked highest. To summarize; Most support for 1E products is achieved by contacting 1E support directly or from their community forums accessible to customers. Similarly, for Endpoint Manager, one of the greatest sources for support is through the Microsoft Forums. There are specific forms relating to Compliance Settings, and posts there are monitored daily by Microsoft staff, MVPs and community experts. Comparatively, support for custom industry PowerShell Desired State Configuration Modules is the responsibility of the Vendor or Author of the solution. And for Group Policy, Microsoft limits the support of Group Policy objects to their own policies. If a vendor has created a custom Group Policy Extension or solution, they will support it. Microsoft can help troubleshoot the core Group Policy Engine, but the overall scope of support would have to be a unified effort.
You can read the full comparison report and learn how the vendors stack up for other evaluation criteria, here. To learn more, be sure to check out Part 1, Part 2, Part 3, and Part 4!