Hello again. It's John DeVito, 1E Senior Customer Success Architect, with another blog post. This time I want to look at some points in the typical Linux user lifecycle. The lifecycle starts with things like account creation and proceeds through various tasks to the deletion of the account. In this blog we'll cover the creation of an account.
The Linux Account Management product pack, available on the 1E Exchange, contains 23 instructions. Some are highlighted here to showcase how to manage the user account lifecycle on Linux devices in your environment. While some of the items discussed will deal with group membership additions and removal, another blog will address some additional items specific to group account management.
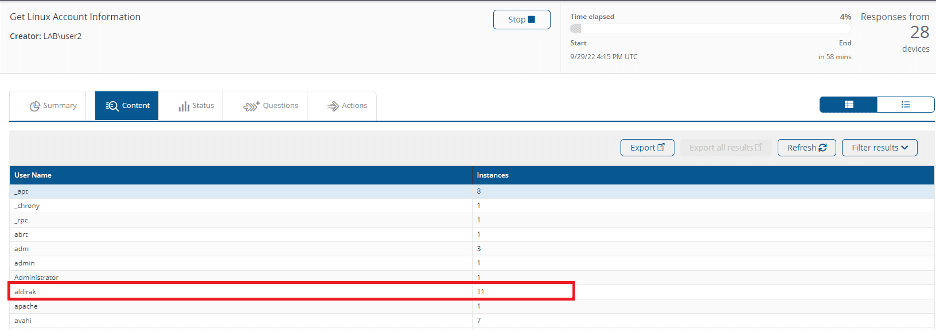
There's a need to create a user named "aldirak" in the environment. First, we'll run the "Get Linux Account Information" question to find out if it already exists on devices.
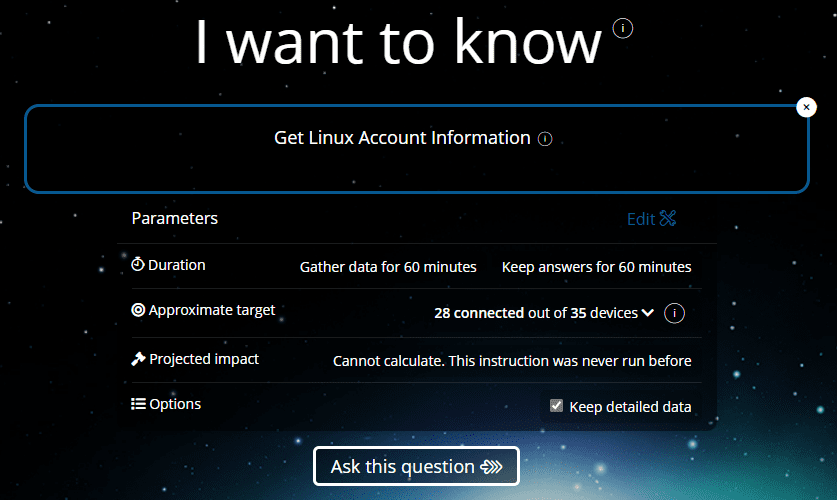
This instruction will report back to us what accounts already exist in the environment and on which devices the accounts exist. The output is sorted by user account names in alphabetical order, and aggregated by User Name. The Instances column shows how many devices have an account for each existing user name.
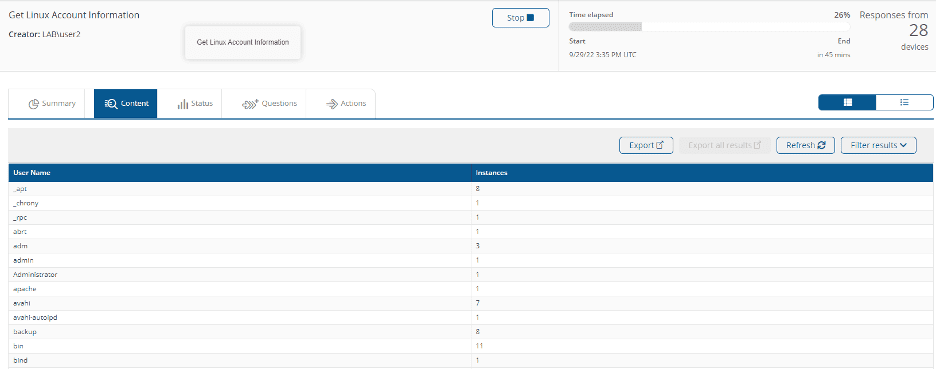
Searching the list we can see that the user "aldirak" doesn't already exist on any device in the environment. It's not a problem if the user exists. The instruction to create a user account will detect that the account already exists. And on devices where the account exists, the instruction exits without taking any further action.
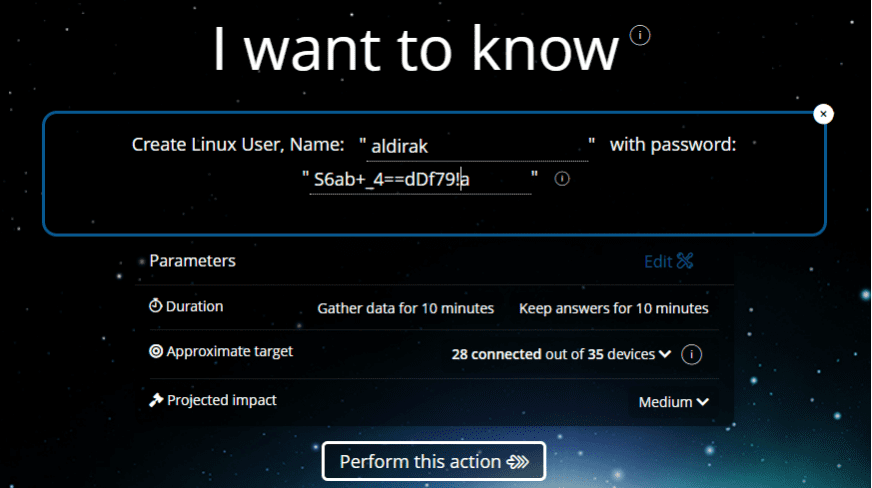
Running the "Create Linux User" instruction, and specifying the username and an initial password, creates the user account on the targeted devices. As always, since this is an action that'll make a change on the targeted endpoints, approval is required.
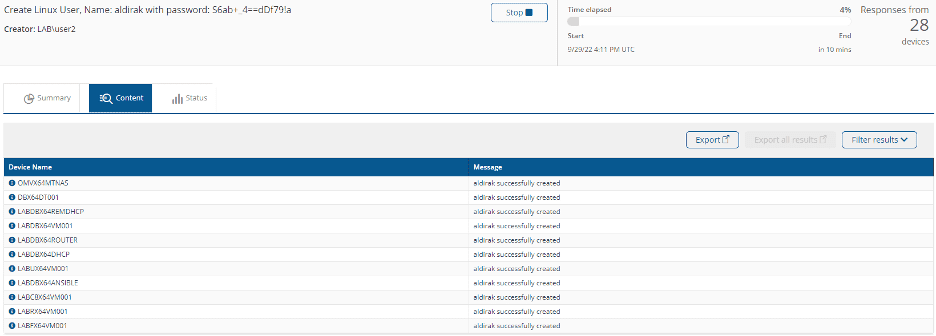
Once the instruction is approved, the output shows that the account was created on the targeted devices.
Revisiting the "Get Linux Account Information" instruction, "aldirak" shows up in the list now.
Clicking on the "aldirak" username, the devices where the account now exists—along with parameters associated with the account—can be identified. You'll notice that the list of devices where the account exists matches the list of devices returned by the "Create Linux User" instruction. 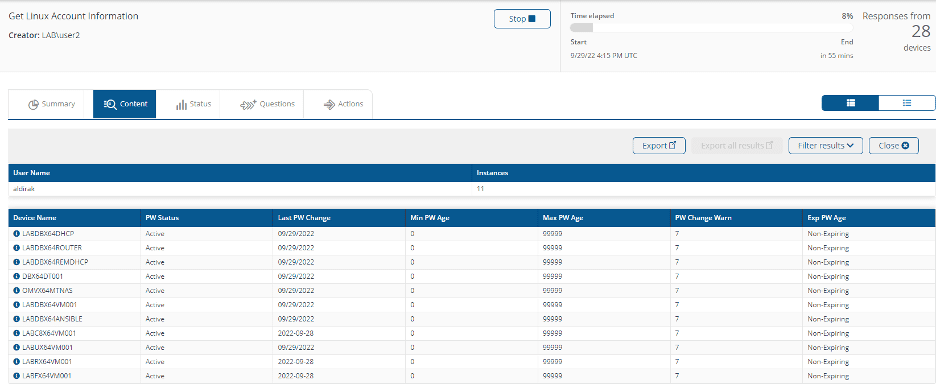
There's also a "Set Parameter for User" instruction in the product pack which allows an admin to modify the values for the "Minimum Password Age", "Maximum Password Age", "Password Change Warning", and "Expired Password Age" values.
A "Password Status" value of "Active" means the account is "live" and ready to use. The account can be locked using the "Lock Account for Linux User" instruction in the product pack.
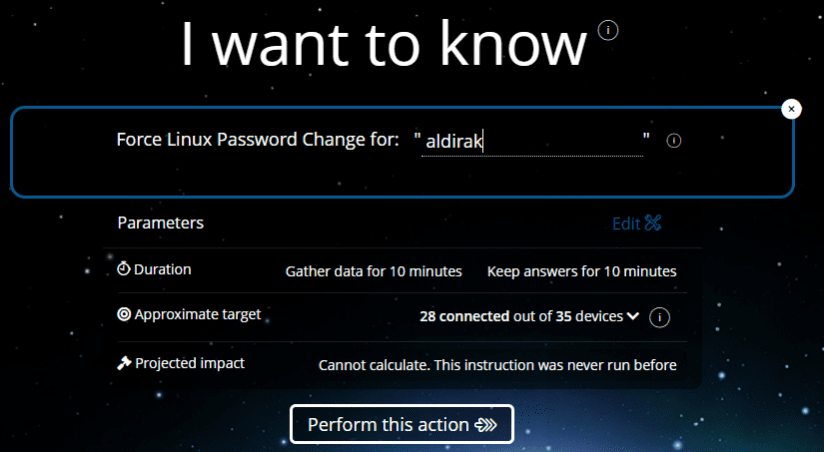
One thing that you've surely noticed is that I created an account with a password. You may be wondering if the user will be forced to change the password. There's an additional instruction to force the user to change the password. It's "Force Linux Password Change", which can be run before the creation of the account is ever communicated to the end user. Supply the username to flag the account for a forced password change.
The output of the instruction will indicate the password has a status of "expired" for the account and will force the user to change the password. This can be done at creation of the account, or at any time when it's required to force a user to change their password.
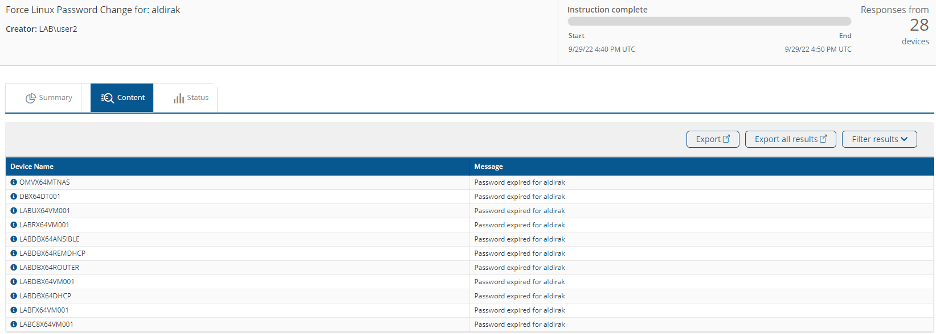
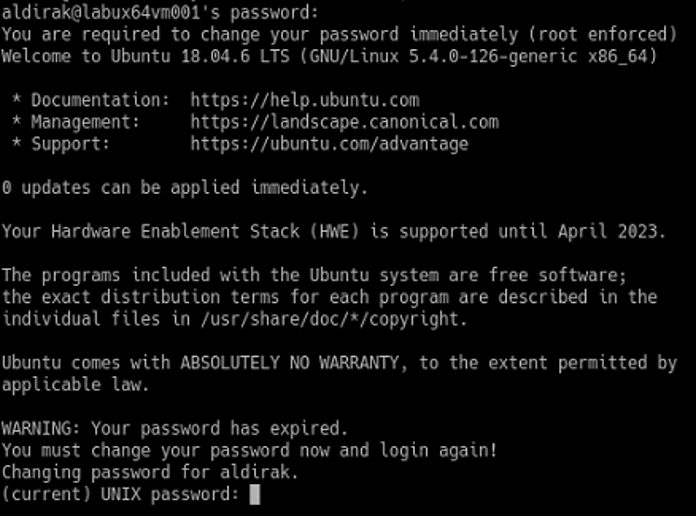
I forced Kerrie ("aldirak") to change their password, and, for example, upon logging into a RedHat server, they're greeted with a message to this effect.
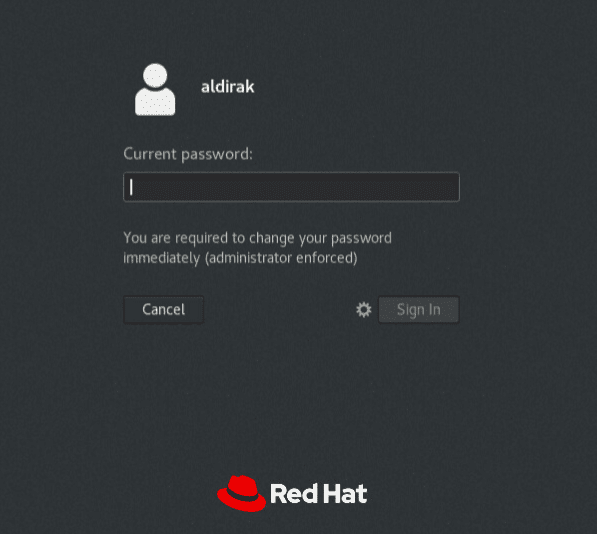
This was tested with RedHat, Debian, Ubuntu, Fedora, CentOS, openSUSE, and SLES distros from both UI and Console based sessions. When forcing a password change, it seems to work best when using a console session on Debian-based distros.
If you're interested in learning more about Linux repositories and updates, you can check out part one and part two of this series!



