May is off to a rocky start. This new breed of cyber attacks is troubling to say the least.
Since the beginning of the month, the world has seen some terrifying new security breaches. For the first time in history, a country has operated in real-time against a cyber attack or threat using military force. This is where we are now.
As we've said multiple times over the last few years, cybercriminals aren't going into hiding. They're getting slicker, savvier, and more dangerous. Most of them are playing the long game and waiting for the right time to strike.
From Burger King to GitHub, let's take a look at some of the worst cyber attacks that have happened in only 8 days.
-
Burger King
It seems as if you can't even get a burger these days without it coming with something that wasn't on the menu. This breach exposed over 38,000 records of data containing information about children. PII such as email addresses, names, phone numbers, and even their DOB was compromised. The database, ElasticSearch, is well known for being able to house lots of records in an unprotected format.
-
GitHub
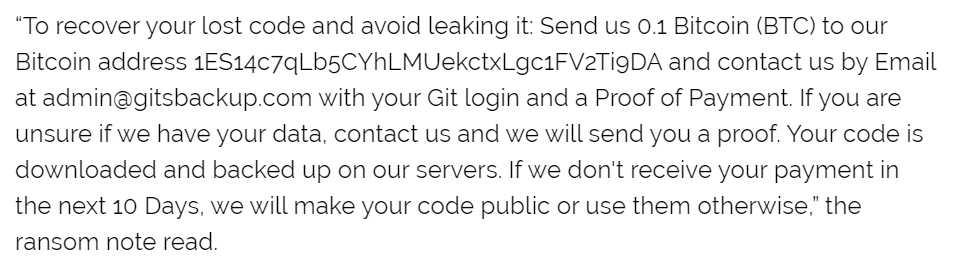
Techies everywhere have lost their tempers as the latest targeted attack on GitHub, GitLab, and Bitbucket has seen user's data erased and replaced with a ransom note.
-
Airbnb
Congratulations! You're going on vacation! Oh? You didn't know? Yeah, you're amongst the thousands of users who had random reservations booked in their name. Other users reported their reservations as canceled, and then subsequently charged a cancellation fee. Some even had their entire accounts deleted! Kiss that tropical tree-house vacay goodbye.
-
E
GE's Power Meter software has seen better days. Several vulnerabilities have been spotted which could allow bad actors to plant malicious files which grant them admin privileges.
Clearly, there is a security hygiene problem that still needs to be addressed. We've recently written an eBook that directly confronts this problem.




