Tachyon, strictly speaking, is a platform of capabilities. It isn’t an “Ops” tool or a “Security” tool—it’s a platform that has a ton of capabilities, which in turn provide for many endpoint management functions that provide customer value. That value may be in the form of increased security, and/or easier faster IT operations, and/or improved end-user experience.
One of the key features of Tachyon is its real-time nature. Being able to have an endpoint perform an action in the blink of an eye makes for some interesting use cases.
I recently stumbled across this graph, from a recent report by Anti-Malware player Coveware:
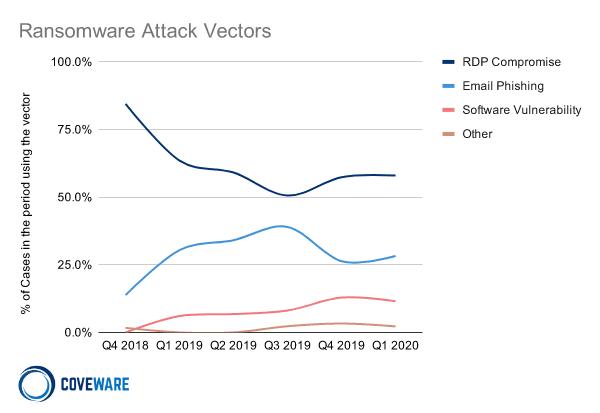
I knew from previous analysis in the Verizon DBIR report that RDP was a super prevalent attack vector – but I never would have expected it to be responsible for more Ransomware than Phishing!
Mitigating the risks of RDP with Tachyon
I’ve covered this before in 2017 and in 2018. Leaving RDP open all the time is a bad idea and it isn’t needed any more. You can access a device, on-demand, in real-time, using RDP, even if that device wasn’t running RDP 5 seconds ago.
To put that another way: you can disable RDP, ergo mitigating the risks it poses and still use it. That may sound like an oxymoron (use the disabled protocol) but the difference is Tachyon.
With Tachyon, you can enable the protocol in real-time, and indeed enable functions like admin rights, also in real time, when you need them; even a second before you make connection to the box (or during the same second!).
But there’s also another way…
One of our customers (with 28,000 endpoints in the electronics world), let’s call him “Mark”, once told me that they felt like a failure if they had to RDP into a machine now. The reason is twofold:
- Tachyon allows you to do SO many different things on an endpoint, that your need to RDP into devices becomes minimal
- If there was something that Mark wanted to do which wasn’t already there, they took the 5 minutes to create a new Tachyon instruction rather than just RDP’ing in directly. They did this so that others could perform that operation through Tachyon in future, rather than “bothering” Mark to go and RDP in again in future.
When you create a Tachyon instruction for something, others can execute it with ease in future – creating ever fewer reasons to NEED to RDP into a device.
You can see some videos in the 2017 and 2018 blog posts linked above. In the next blog in this series, I’ll show you how this has been improved over the past few years and how several customers are using Tachyon today to mitigate against the risks RDP poses, while still using everyone’s favorite Remote Desktop Protocol… but hopefully less and less often as automation increases!




